Microsoft Ftp Service Exploit
- Microsoft Ftp Service Exploit Windows 10
- Microsoft Ftpd Exploit
- Microsoft Ftp Service Exploit Free
- 220 Microsoft Ftp Service Exploit Metasploit
- Microsoft Ftp Client
| CVSS Meta Temp Score | Current Exploit Price (≈) | CTI Interest Score |
|---|---|---|
| 7.2 | $0-$5k | 0.27 |
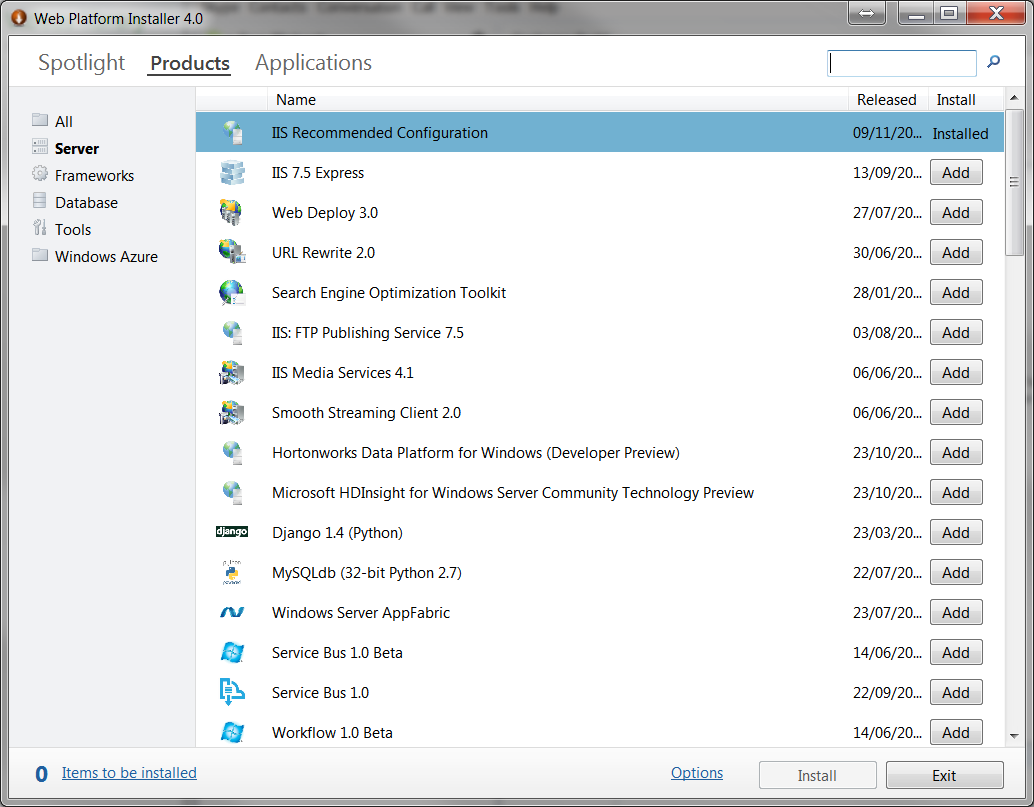
A vulnerability has been found in Microsoft IIS 7.5 (Web Server) and classified as critical. This vulnerability affects some unknown processing of the component FTP Server. The manipulation as part of a Telnet IAC Character leads to a memory corruption vulnerability. The CWE definition for the vulnerability is CWE-119. As an impact it is known to affect availability.
8 The ProFTP server (192.168.79.135) was started in debugging mode and was accessed from the Windows machine (192.168.79.1) using the in-built Windows ftp command. The user prithak (having password prithak) was able to successfully log into the ProFTPD server and at the same time the ProFTPD server produced debugging logs on the standard. Regularly updating FTP credentials can help deter a Dridex-based exploit. FTP servers alone lack the system capabilities that many organizations need to meet today’s business requirements. From security, productivity, and compliance, an FTP server by itself can’t scale to either cost or complexity.
- This module exploits a stack buffer overflow flaw in the Microsoft IIS FTP service. The flaw is triggered when a special NLST argument is passed while the session has changed into a long directory path. For this exploit to work, the FTP server must be configured to allow write access to the file system (either anonymously or in conjunction with a real account).
- 220 Microsoft Ftp Service X0d X0a Exploit Microsoft IIS FTPd NLST Remote Buffer Overflow Vulnerability Microsoft IIS is prone to a remote stack-based buffer-overflow vulnerability affecting the application's FTP server. An attacker can exploit this issue to execute arbitrary code within the context of the affected application.
The issue has been introduced in 07/22/2009. The weakness was shared 12/22/2010 by Matthew Bergin (Website). The advisory is available at exploit-db.com. This vulnerability was named CVE-2010-3972 since 10/14/2010. The attack can be initiated remotely. No form of authentication is required for a successful exploitation. Technical details are unknown but a public exploit is available.
A public exploit has been developed by Matthew Bergin in Python and been published even before and not after the advisory. It is declared as highly functional. It is possible to download the exploit at securityfocus.com. The vulnerability was handled as a non-public zero-day exploit for at least 518 days. During that time the estimated underground price was around $5k-$25k. The vulnerability scanner Nessus provides a plugin with the ID 51904 (MS11-004: Vulnerability in Internet Information Services (IIS) FTP Service Could Allow Remote Code Execution (2489256)), which helps to determine the existence of the flaw in a target environment. It is assigned to the family Windows : Microsoft Bulletins and running in the context local.
Upgrading eliminates this vulnerability. Applying a patch is able to eliminate this problem. The bugfix is ready for download at blogs.technet.com. The best possible mitigation is suggested to be upgrading to the latest version. A possible mitigation has been published 2 months after the disclosure of the vulnerability. Furthermore it is possible to detect and prevent this kind of attack with TippingPoint and the filter 10812.
The vulnerability is also documented in the databases at SecurityFocus (BID 45542), X-Force (64905), Secunia (SA42713), SecurityTracker (ID 1024921) and Vulnerability Center (SBV-28789).
Product
Type
Vendor
Name
CPE 2.3
CPE 2.2
CVSSv3
VulDB Meta Base Score: 7.5VulDB Meta Temp Score: 7.2
VulDB Base Score: 7.5
VulDB Temp Score: 7.2
VulDB Vector: 🔍
VulDB Reliability: 🔍
CVSSv2
| AV | AC | Au | C | I | A |
|---|---|---|---|---|---|
| 🔍 | 🔍 | 🔍 | 🔍 | 🔍 | 🔍 |
| 🔍 | 🔍 | 🔍 | 🔍 | 🔍 | 🔍 |
| 🔍 | 🔍 | 🔍 | 🔍 | 🔍 | 🔍 |
| Vector | Complexity | Authentication | Confidentiality | Integrity | Availability |
|---|---|---|---|---|---|
| unlock | unlock | unlock | unlock | unlock | unlock |
| unlock | unlock | unlock | unlock | unlock | unlock |
| unlock | unlock | unlock | unlock | unlock | unlock |
VulDB Base Score: 🔍
Microsoft Ftp Service Exploit Windows 10
VulDB Temp Score: 🔍
VulDB Reliability: 🔍
NVD Base Score: 🔍
Exploiting
Class: Memory corruptionCWE: CWE-119
ATT&CK: Unknown
Local: No
Remote: Yes
Availability: 🔍
Access: Public
Status: Highly functional
Author: Matthew Bergin
Programming Language: 🔍
Download: 🔍
Price Prediction:
 🔍
🔍Current Price Estimation: 🔍
| 0-Day | unlock | unlock | unlock | unlock |
|---|---|---|---|---|
| Today | unlock | unlock | unlock | unlock |
Nessus ID: 51904
Nessus Name: MS11-004: Vulnerability in Internet Information Services (IIS) FTP Service Could Allow Remote Code Execution (2489256)
Nessus File: 🔍
Nessus Family: 🔍
Nessus Context: 🔍
OpenVAS ID: 901183
OpenVAS Name: Internet Information Services (IIS) FTP Service Remote Code Execution Vulnerability (2489256)
OpenVAS File: 🔍
OpenVAS Family: 🔍
MetaSploit ID: iis75_ftpd_iac_bof.rb
MetaSploit Name: Microsoft IIS FTP Server Encoded Response Overflow Trigger
MetaSploit File: 🔍
Exploit-DB: 🔍
Threat Intelligence
Threat: 🔍Adversaries: 🔍
Microsoft Ftpd Exploit
Geopolitics: 🔍
Economy: 🔍
Predictions: 🔍
Remediation: 🔍
Countermeasures
Recommended: UpgradeStatus: 🔍
Reaction Time: 🔍
0-Day Time: 🔍
Exposure Time: 🔍
Patch: blogs.technet.com
TippingPoint: 🔍
McAfee IPS: 🔍
McAfee IPS Version: 🔍
ISS Proventia IPS: 🔍
PaloAlto IPS: 🔍
Fortigate IPS: 🔍
Timeline
07/22/2009🔍10/14/2010+449 days🔍
12/21/2010+68 days🔍
12/21/2010+0 days🔍
12/21/2010+0 days🔍
12/21/2010+0 days🔍
12/22/2010+1 days
Microsoft Ftp Service Exploit Free
🔍12/22/2010+0 days🔍
12/22/2010+0 days🔍
12/22/2010+0 days🔍
12/23/2010+0 days🔍
12/26/2010+3 days🔍
01/19/2011+24 days🔍
02/08/2011+20 days🔍
02/08/2011+0 days🔍
04/17/2016+1895 days🔍
03/12/2017+329 days🔍
Sources
Vendor: https://www.microsoft.com/Advisory: exploit-db.com
Researcher: Matthew Bergin
Status: Confirmed
CVE: CVE-2010-3972 (🔍)
OVAL: 🔍
SecurityFocus: 45542 - Microsoft IIS FTP Service Remote Buffer Overflow Vulnerability
Secunia: 42713 - Microsoft IIS FTP Server Telnet IAC Character Encoding Vulnerability, Highly Critical
X-Force: 64905
SecurityTracker: 1024921 - Microsoft IIS FTP Server Lets Remote Users Deny Service
Vulnerability Center: 28789 - [MS11-005] Microsoft Internet Information Services 7.5 Remote Arbitrary Code Execution Vulnerability, Critical
OSVDB: 70167 - Microsoft IIS FTP Server Telnet IAC Character Handling Overflow
Vupen: ADV-2010-3305
scip Labs: https://www.scip.ch/en/?labs.20161013
Entry
Created: 01/19/2011 01:00 AMUpdated: 03/12/2017 08:46 AM
Changes: (22) vulnerability_cvss2_nvd_av vulnerability_cvss2_nvd_ac vulnerability_cvss2_nvd_au vulnerability_cvss2_nvd_ci vulnerability_cvss2_nvd_ii vulnerability_cvss2_nvd_ai advisory_disputed exploit_availability exploit_date exploit_publicity exploit_url exploit_developer_name source_osvdb_create source_secunia_date source_securityfocus_date source_securityfocus_class source_sectracker source_sectracker_date source_sectracker_cause source_vupen source_exploitdb source_exploitdb_date
Complete: 🔍
Enable the mail alert feature now!
Severity: High 8 February, 2011 Summary: This vulnerability affects: The IIS FTP service running on Windows Vista, 2008, 7, and 2008 R2 How an attacker exploits it: By sending a specially crafted FTP command Impact: In the worst case, an attacker gains complete control of your IIS server What to do: Deploy the appropriate IIS [].
The best posible result is TERE BINA TERE BINA DIL NAHI LAGDA BY RAHAT FATHE ALI KHAN that has been uploaded by AZ5JUTT786 and Tere Bina Song| Tezz| Ajay Devgan & Kangna Ranaut| Rahat Fateh Ali Khan probably the last item we have been found. You can download best quality Tere Bina Dil Nahi Lagda mp3 incuding 320kbps. Tere Bina Song| Tezz| Ajay Devgan & Kangna Ranaut| Rahat Fateh Ali Khan - mp3 by VENUS MOVIES Bitrate 128kbps|| Frequency 44100 Hz You are searching for Tere Bina Dil Nahi Lagda mp3 songs download. We have found total 14 songs. Soniye dil nahi lagda tere bina female mp3 download. Tere Bina Dil Nahi Lagda free mp3 download, Tere Bina Dil Nahi Lagda free mp3 download 320kbps, Tere Bina Dil Nahi Lagda free mp3 download mp3lio, Tere Bina Dil Nahi Lagda song download mp3, Tere Bina Dil Nahi Lagda mp3 song free download, Tere Bina Dil Nahi Lagda audio download, Tere Bina Dil Nahi Lagda mp3 download skull,Tere Bina Dil Nahi Lagda free mp3 download lyrics.
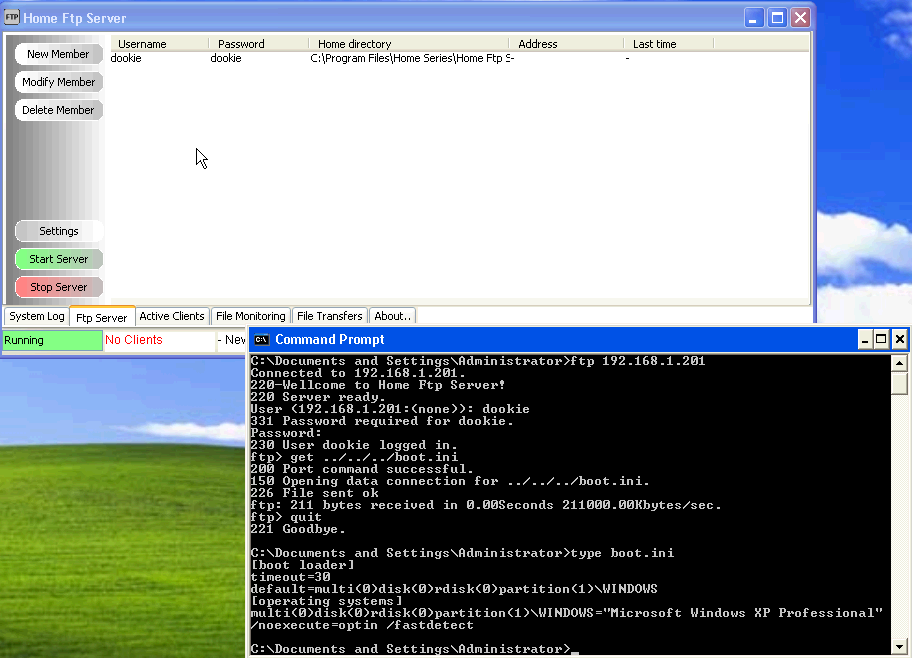
FTP is a service that is commonly used in Web Servers from Webmasters for accessing the files remotely.So it is almost impossible not to find this service in one of our clients systems during an engagement.
For that reason we will try to cover in this article a scenario of a possible attack against the FTP Server.
The first thing that we need to do is of course to identify which systems are running the FTP service (for the needs of this tutorial I have put only one system). We can do a simple scan with Nmap in order to find the open ports.
We can see that the FTP port is open. Now the next logical step that we have to do is to identify which version the FTP application is running by using a method which called FTP banner grabbing.
Of course we can use the Nmap for the discovery of the remote operating system and the service fingerprinting but in this tutorial we will not take advantage of that.
Banner Grabbing is a technique that someone can use in order to extract information from application banners.For example if the remote host is a web server,we can try to connect through telnet.The banner results will give us an indication about the operating system and the type of the web server (Apache or IIS).
Command: telnet target_IP 80
In order to do a banner grabbing in the FTP service we will just try to connect through our console to the FTP server.
FTP Banner Grabbing
From the above image we can see that the version is 1.3.1 and the operating system is Debian.There are many things that we can do from here.First we can try to find if there is any public exploit for the ProFTPD 1.3.1 version.If there is then we can launch it against the FTP Service.
If there is not any public exploit for the specific version then we can try to find a valid username and password by using a dictionary attack.We can use any tool like THC Hydra for this job but in this article we will see how it could be achieved through metasploit.
Metasploit Framework has a specific module for attacking FTP servers.So we will search on the metasploit for the module ftp_login.
Now that we have found the FTP scanner it is time to configure it.Of course we will need some good wordlists for the usernames and the passwords.If we don’t have then there is no problem because metasploit has a folder with various wordlists.Here we will use the wordlists that contains Unix usernames and passwords.
We are setting the scanner according to the following image and we type run in order to the scanner to start:
FTP Scanner Settings
The scanner has discovered 3 valid login credentials as you can see from the next 3 images.
Discovery of the service username/password
So now we have three valid logins to choose in order to connect to the FTP server.Lets try the last one which is the user as username and user as password.
Login with a valid account on the FTP server
We can see that we have successfully managed to login to the FTP server.Now we can execute the command ls -lat to the server in order to display the list with the current directories and subdirectories and the permissions that we have on the directories.
There are two directories that are important here.The SSH because it may contain private SSH keys and the bash_history because it keeps a history of all the commands that the user has run.For example you can find information about user ID,passwords,confidential file names,locations,server names and shared folders.
We will download the bash_history file to our computer with the command get as you see it in the image below:
Download the file to our computer
220 Microsoft Ftp Service Exploit Metasploit
Except of the console for the connection to the FTP server we can use also our browser.We will try to login with the same credentials user/user
After some searching in the directories we have found a directory which contained the following:
Directory of usernames
We can see that there are 4 folders.A folder named user, a folder named service and a folder named msfadmin.
Microsoft Ftp Service
This is an indication that another account exists under the username msfadmin which probably is an administrator’s account and has more privileges.The reason that we assumed that is because the folders names are the same with the usernames that we have discovered previously.
The previous accounts had passwords same with the usernames.So we will try to login with the following credentials:
Username: msfadmin
Microsoft Ftp Client
Password: msfadmin
The image above is showing that our try to login with the username/password msfadmin was successful.If the password was different then we could have tried another dictionary attack against the FTP server in order to find and the password.
So we have managed to login to the FTP server with an administrator’s account.
Conclusions
There are some conclusions that we can make regarding this scenario.First of all the banner grabbing allow us to discover valuable information about the FTP server and the target operating system.This means that if the administrator had changed the FTP banner then it would be much harder for us to disclose these information.
In addition we have noticed the weak credentials of the 3 accounts that we discovered.Also the administrator’s account password is the same with the username.This account policy is unacceptable in most of the companies and probably you will not meet something similar.However even large organizations are suffering from weak passwords so eventually it can happen.It is important for that reason to have a good password policy.
On the other hand if a malicious user was trying brute force or dictionary attacks (like this scenario) against the FTP server then it would probably flooded the log files.A security solution that would block the IP address after 3 unsuccessful logins would be the most effective.
Microsoft Ftp Service 5.0 Exploit
